Zero Trust Architecture
Zero Trust ArchitectureTrust nothing; verify everything.
Zero Trust ArchitectureTrust nothing; verify everything.

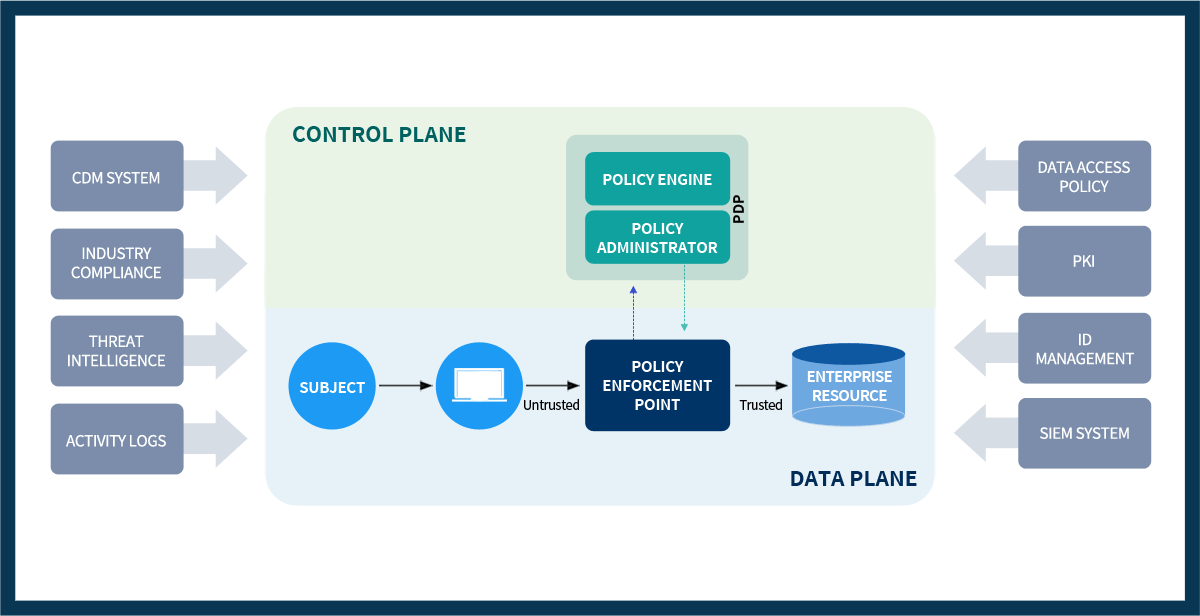
Logical components of Zero Trust Architecture
Continuous Diagnostics and Mitigation (CDM)
Threat intelligence feed(s)
Network and system activity logs
Security Information and Event Management (SIEM)